THERE was a cyber attack on BankIslami last week that cost them Rs2.6 million. While the amount was rather modest, the incident rang alarm bells regarding information security measures within the financial sector, exposing further vulnerabilities.
As a precautionary measure, around 10 local banks blocked international transactions on their debit and credit cards.
With that, a possible crisis seemed to have been averted but on Nov 4, a report by PakCert— a local cyber security company—on a data breach involving 20,000 Pakistani bank accounts started making the rounds across all media, causing panic amongst everyone, from bankers to consumers.
The ‘PakCERT Threat Intelligence Report’ claimed that on Oct 26, there was a data dump of 9,000 bank account details—including full name, card number and CVV among others—on the darknet. A second dump occurred, this time involving 11,000 Pakistani cards from 21 banks, on Oct 31. The Federal Investigation Agency confirmed this, while the State Bank of Pakistan (SBP) denied the allegation straight out, calling them mere rumours.
The Pakistan Banks’ Association on Nov 7 also gave its official statement regarding the matter. Giving further weight to the SBP, the banks’ body said that IT security of only one bank had been breached. It also pointed out the difference between fraudulent transactions and a security breach: the former can be done without compromising the IT security of a bank.
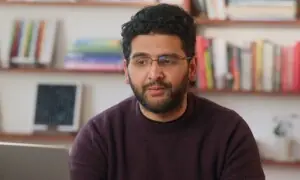
And this is exactly what a cyber security expert Dawn spoke to said. “The attack on BankIslami was very sophisticated — Advanced Persistent Threat (APT), as we call it — even though the loss was pretty small.
“As for the darknet dump reports, it could be that account details were stolen through compromised individual browser histories and other fraudulent activities, which obviously has nothing to do with banks’ cyber security system.
“There was no breach on other banks, only that the dump took place recently while the information was collected a long time back,” explained Muhammad Abbas Rajani, CTO of DigitLabs, a local software and security solutions firm.
A very good example of APT would be the cyber heist at Bangladesh Central Bank in 2016 that attempted to transfer $1 billion to the New York Federal Reserve and was successful in stealing $81m. “These hackers study the system, observe patterns for months and bypass security measures; a ‘skid hack’ is generally basic,” he says.
Hence, while the claim that a data breach of most Pakistani banks took place seems to be false, it has nonetheless raised flags within the sector.
The SBP also mandates on issues regarding cybersecurity. So far, the central bank has mostly provided guidelines through various circulars, such as subjecting all banks and development finance institutions to an annual external audit of their IT security system.
However, much of that is limited to best practices and implementation eventually comes down to individual discretion of these companies. “There is actually a lot of investment in IT security by these organisations and in my experience, the standards are fairly high within finance, especially compared to other sectors like pharmaceuticals or insurance,” says Mr Rajani.
“They usually buy the most expensive or best system but the processes and implementation are generally weak and even the people in charge often don’t have the right skill set. If the processes are kept tight, even with a cheaper system, there is a 70-80 per cent chance of containing threats.”
A national-level watchdog or regulator would go a long way to ensure process competency, similar to what Computer Emergency Response Team in India does. “Such a body can set the standards for all sectors which can then be coordinated by other regulators like the SBP,” Mr Rajani concludes.
In Pakistan the organisation currently overseeing cyber crime is National Response Centre for Cyber Crime, but its role has been rather limited to dealing with cyber bullying or harassment—nothing nearly sophisticated enough to counter APTs.
No wonder then that in the 2017 Global Cybersecurity Index, the United Nations International Telecommunication Union ranked Pakistan 67th, compared to Bangladesh at 53 and India 23.
In the technical head, the country was placed in the “initiating” category for two components relating to the private sector—“Standards for Organisations” and “Standards for Professionals” while also faring poorly in terms of “Standardisation Bodies” and “R&D” programmes, amongst others.
Published in Dawn, The Business and Finance Weekly, November 12th, 2018