ISLAMABAD: A recent survey titled “Cybersecurity in the Workplace: Employee Knowledge and Behaviour” shows that 39pc of professionals in Pakistan consider their company’s cybersecurity rules excessive or not fully appropriate, while 8pc say their organisations either lack such rules or they are unaware of them.
The survey, conducted by cybersecurity company Kaspersky, highlights a disconnect between corporate policies and employee adherence, underscoring risks linked to shadow IT and unmanaged device usage.
According to the report, 38pc of respondents said there are no policies governing the use of non-corporate devices. Meanwhile, 17pc admitted they can use personal devices to access business information if these have some form of cybersecurity protection, even consumer-grade software.
On the positive side, 16pc said personal devices must pass stringent corporate IT security checks before use, while 29pc reported that only company-issued devices are permitted for work.
The situation is relatively better when it comes to installing software on corporate devices. Around 56.5pc said only IT specialists are allowed to install software, while 19.5pc reported that only top management or designated users have such permissions. Another 17pc said employees can install software approved by the IT team. However, 7pc noted that all users can install any software without IT approval.
At the same time, 26pc of professionals acknowledged installing software on work devices without IT supervision in the past year, highlighting a persistent shadow IT challenge that exposes organisations to security vulnerabilities, compliance risks and data breaches.
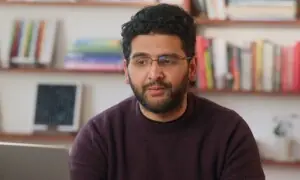
“Shadow IT is now a mainstream operational risk. When one in five employees installs software without IT oversight, it signals a policy gap,” said Toufic Derbass, Managing Director for the META region at Kaspersky. He stressed that organisations must move beyond restrictive controls and adopt user-centric cybersecurity strategies that integrate technology with employee awareness and responsible use.
To strengthen defences, the report recommends conducting shadow IT audits to identify unauthorised software, cloud services and personal devices accessing corporate data, alongside implementing robust monitoring and cybersecurity solutions.
It also advises that where personal device use is permitted, organisations should define clear minimum security requirements and enforce them through mobile device management or endpoint management tools, complemented by employee training on real-world risks.
Published in Dawn, April 26th, 2026