KARACHI: Someone inside Pakistan purchased an estimated 300,000-euro toolset of highly controversial surveillance software, and digital human rights activists are concerned about the serious threats this poses to the security and privacy of users operating in local cyberspace.
Digital Rights Foundation Pakistan (DRFP), a local NGO focused on digital rights, released its investigation into a 40GB leak of data from the servers of FinFisher, an online mass surveillance software that has been criticised by human rights organisations for its high potential for abuse, as in its use to target protesters in Bahrain (2012) and its purchase by Egyptian secret services during the revolution of 2011.
The latest data leak this August was made downloadable online by a hacker identified only by the online handle, PhineasFisher. The hacker wrote a note on social networking site Reddit, justifying the leak as a means to, “hopefully develop a better understanding of the organisations, and methods of operation involved in these [surveillance] attacks so that those targeted can actually defend themselves.”
DRFP carried out an investigation into the data, given the fact that tests carried out in 2013 by Canada-based Citizen Lab confirmed the presence of two FinFisher Command and Control servers operating in Pakistan.
DRFP sifted through the new data which included correspondence between customers and FinFisher support staff, and found that someone from Pakistan licensed three softwares from FinFisher for a period of three years. FinSpy and FinUSB were purchased by the Pakistani customer in April 2010, while the FinIntrusion Kit was purchased in June 2010.
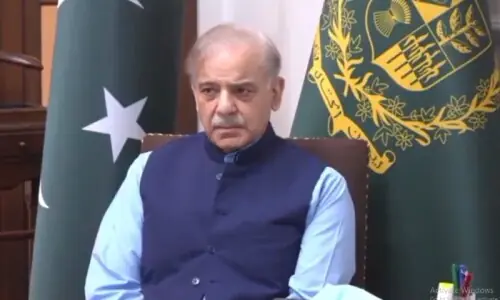
 |
| The screenshot of the FinFisher portal shows the software purchases made by the Pakistani customer, including license validity period. |
Also read: PTA says it does not conduct surveillance
FinSpy is used to remotely control and access online users who “change location, use encrypted and anonymous communication channels and reside in foreign countries”. FinUSB is used to infect USB devices, so whoever uses them becomes a target of surveillance, while the FinIntrusion Kit makes it possible to hack into hotel, airport, and other Wi-Fi networks to record traffic, extract usernames and passwords (even for encrypted sessions), and capture data like webmail, video portals, online banking and more.
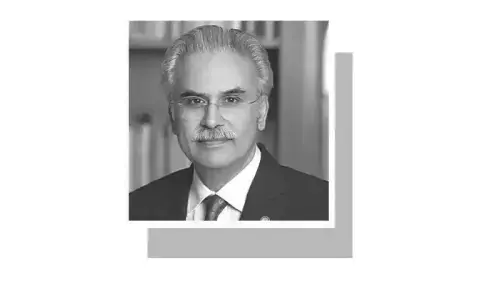
 |
| The screenshot shows an online complaint filed by the Pakistani customer, which is responded to by FinFisher Customer Support. |
Chats between “Customer 32” (username 0DF6972B and ID 32) who identifies himself as ‘Khalid’ from Pakistan, and FinFisher support staff indicate that the surveillance software was being used to infect Microsoft Office PowerPoint documents to enable spying on whomever received and opened the file(s).
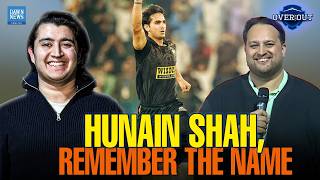
 |
| The screenshot of the FinFisher portal shows a software update request by the Pakistani customer. |
Additionally, the DRFP report cites that, “Customer 32 also used FinFisher to covertly steal files from target” computers.
All the files of those who were targeted were readily available but Customer 32 wanted more. As outlined in another exchange with FinFisher support staff, ‘Khalid’ requested a software update where: “the agent [should] be able to select files to download even when the target is offline and whenever the target comes online, those selected files may be downloaded without the interaction required from user.”
DRFP alleges that the spy software was likely being used by a Pakistani intelligence agency, given the high cost of the software and the fact that FinFisher’s company policy states that, “solutions are sold to governmental agencies only”.
Director of DRFP Nighat Dad terms these findings “worrisome” due to the human rights violations associated with this technology.
“Vulnerable groups like human rights defenders, journalists and activists are at great risk in Pakistan, where there are no protections of privacy rights and no regulations being followed in the surveillance of people,” says Ms Dad, adding that, “As citizens of a democratic state, it is our right to know who is using such intrusive surveillance software in Pakistan, and what laws and regulations are being followed in their deployment.”
Court case against FinFisher use in limbo
Based on Citizen Lab’s earlier findings, digital rights organisation Bytes For All Pakistan filed a public interest litigation case in the Lahore High Court in May 2013, challenging the existence of FinFisher Command and Control Servers in Pakistan. The same month, the Lahore High Court ordered the Pakistan Telecommunication Authority to present a report on the issue within 30 days. Over a year has passed, with six “confirmed dates”, but the PTA has yet to produce the report, and the court has yet to proceed on the case.
Lamenting the lack of action, petitioner and Bytes for All chairman Shahzad Ahmad says, “There is ample evidence already since the Citizen Lab report, so no more investigation is needed. There is hard technical evidence. Right now, we need a response from authorities in the court of law.”
With proof that FinFisher has been and may still be active in Pakistan, Ahmad says the issue of online surveillance is now of greater importance than that of the more high-profile online censorship issues.
“Unfortunately, breach of privacy is a much graver issue than censorship, as censorship can be circumvented; loss of privacy is permanent,” Ahmad says.
Published in Dawn, August 24th, 2014