SO, you receive a WhatsApp call from an unfamiliar number. You choose not to answer it. There’s another call. You still don’t answer. But that’s enough for spyware to be installed on your phone, regardless of whether it’s an Apple or an Android. The days when attempts to instal malware on your device could be thwarted by not clicking on links or attachments in emails of dubious origin are a thing of the past. Welcome to the world of zero-click attacks.
If the spyware is sophisticated, it can not only mine all the data on your device and monitor your messages and phone conversations, it can also turn on the camera and microphone without the user’s knowledge. In some cases, the hacker can have greater control over the device than the user does.
That level of sophistication is, thus far, not commonplace. But it has been achieved by the Pegasus software that has stirred a storm of indignation across the globe, amid evidence that it was deployed against activists, journalists, and political opponents of regimes friendly to Israel.
That leaves out Pakistan, so far. There’s apparently evidence that the targets included Imran Khan and various other Pakistanis, but with little clarity about who was interested in their activities and exchanges.
Israel aids malicious allies with spyware.
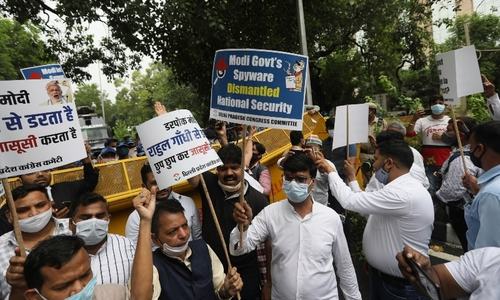
Suspicion will inevitably fall on India — in this case plausibly, given there’s little doubt that Pegasus has been deployed against opponents of the Modi regime, from Rahul Gandhi and his associates to a fairly broad range of activists, lawyers and journalists.
Some of the targets have been named, but it’s an ongoing process, instigated by the Paris-based journalism non-profit Forbidden Stories and Amnesty International, which have shared the fruits of their investigation with a broad bunch of media outlets, from The Wire in India to The Guardian in Britain and Washington Post.
However, the data leak does not reveal the rate of success — it provides only the numbers that were targeted. A forensic analysis of the devices in question is required to determine whether they might have been breached. That’s tricky, because some of the phones used four to five years ago have since been discarded, while in other cases users are reluctant to offer up their devices for examination.
The precise source of the hacking attempts has also not been pinpointed, but the possibilities are limited by the fact that NSO Group, the Israeli firm behind Pegasus, sells its precious spyware only to governments or government agencies. Among the first to acquire the software was the Mexican defence ministry in 2011. The targets included not just the current president of Mexico, Andrés Manuel López Obrador, but also 50 of his family members and associates.
Among the worst consequences was the murder in 2017 of Mexican journalist Cecilio Pineda Birto just hours after he had publicly accused police and politicians of colluding with criminals.
He was gunned down, not chopped up. NSO has long denied its technology was involved in any way with the assassination of Jamal Khashoggi, but Israeli software appears to have helped the Saudi authorities to track his movements and monitor his communications as well as those of his relatives and close associates.
Pegasus spyware: how does it work?
NSO apparently sought to disengage with Saudi Arabia after Khashoggi’s murder but, under new ownership, was persuaded by the Israeli government to re-engage with Riyadh.
The firm’s role in the Khashoggi atrocity and other matters has been questioned before, and it routinely responds with the claim that it sells its spyware only to governments that respect human rights but are seeking help in combating criminality and terrorism. NSO says it is not influenced by the Israeli government which, in turn, alleges it wouldn’t dream of licensing the use of such software for malicious regimes.
Possibly for fear of being decreed anti-Semitic, the outlets reporting the NSO revelations have hesitated to point out that Israel itself incessantly violates human rights, sometimes with fatal consequences for the usually Palestinian victims of its routine brutalisation.
No wonder NSO clients stretch beyond India and Saudi Arabia to Azerbaijan, Bahrain, Hungary, Kazakhstan. Morocco, Rwanda and the UAE which took aim at the innocuous driving rights advocate Loujain al-Hathloul before deporting her to face incarceration — and, allegedly, torture — in Saudi Arabia.
Nor is it surprising that NSO’s outreach is supplemented by other Israeli purveyors of malicious software such as Candiru, Verint, Quadream and Cellebrite. Israeli excellence in software development is no secret; it could be lauded, but for the fact that some of it comes with potential malice aforethought built in.
Mass surveillance is hardly an Israeli innovation, although it’s exceptionally good at it. But its superiority in turning the latest technological advances to the advantage of regimes that thrive on threatening their legitimate opponents disproportionately contributes to an unpalatable global status quo.
Published in Dawn, July 21st, 2021