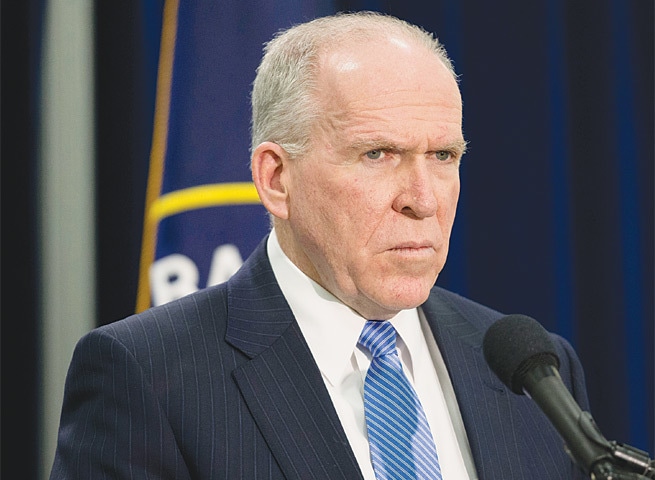
THE world’s most powerful spy, CIA chief John Brennan, was bested on Monday by a self-described “stoner” 13-year-old and an associate, who broke into his America Online (AOL) email account and started posting some of its contents on Twitter. At least some of Brennan’s private emails seemed to contain extremely sensitive information including his security clearance application and the social security numbers of several CIA officers.
Will this cause as much outrage as Hillary Clinton’s private email server (which by the way, was at least more secure than a freaking AOL account)? Almost certainly not! As the architect of the CIA drone programme, Brennan is about as above the law as one could get in the United States. He’s been openly accused of leaking classified information to the press (for which someone else was punished), and he even admitted to orchestrating a “hacking” himself, when he ordered his underlings to spy on the computers US Senate staff members were using to research their damning CIA torture report last year.
You can expect the 13-year-old prankster to get the hammer dropped on him though. As Electronic Frontier Foundation’s Nate Cardozo tweeted, the “CIA Director kept [secret and private] docs on AOL until hacked by a kid. They’re making an example of… the kid”, pointing to an article from the New York Post that reported: “I think they’ll want to make an example out of him to deter people from doing this in the future”, said a source who described the situation as “just wild” and “crazy”.
To add to the embarrassment, the nation’s top Department of Homeland Security (DHS) official Jeh Johnson had a private Comcast account possibly hacked by these same teenagers. It’s worrying that these technologically clueless people are in charge of the nation’s cybersecurity infrastructure. The DHS has been singled out many times for its especially poor cybersecurity practices, despite the fact that they’re supposed to be the federal agency in charge of cybersecurity.
So why does all this matter? Well, it’s all coming against the backdrop of yet another congressional debate about the Cybersecurity Information Sharing Act (Cisa), the dangerous “cybersecurity” bill that’s really a surveillance bill in disguise. The main crux of the bill is to carve a giant exception into all our current privacy laws so as to allow tech companies like Google and Amazon to hand over huge amounts of our information without any legal process whatsoever, as long as they have a vague cybersecurity purpose.
The bill is so bad that the major tech companies like Google and Amazon all came out against it last week, despite the fact that it would give them broad immunity for sharing this information with the government. Also, this bill likely would not have stopped any of the major hacks that have made headlines in the last few months.
Like almost all hacks, Brennan’s started with something incredibly simple: social engineering. Motherboard’s Lorenzo Franceschi-Bicchierai reported that — if we are to believe the hackers — they tricked Verizon and AOL into giving up Brennan’s password by calling their customer service department.
Even “sophisticated” hacks usually involve incredibly unsophisticated methods for initially gaining access to a system, such as social engineering, or phishing (where an attacker sends a malware-filled attachment via email to their victim in the hopes that they download it). As Open Technology Institute’s Robyn Greene wrote recently , 80-90 per cent of cyber-attacks could be prevented or mitigated with basic steps like “encrypting data, updating software and setting strong passwords”. But that’s apparently not what Congress or the intelligence agencies want to hear, knowing that they have an opportunity to legalise a lot more data collection by the National Security Agency.
When a politician inevitably links the hacks of Brennan and Johnson to Cisa in the coming days, remember: the bills would have done nothing to stop it, and we should not be entrusting even more of our private information in the hands of people who can’t even control their own.
—By arrangement with The Guardian
Published in Dawn, October 22nd, 2015
On a mobile phone? Get the Dawn Mobile App: Apple Store | Google Play